The topic of network security has been at the center of attention for some time.
With the advancement of technology and the possibilities offered by the Internet, the risks and the dangers of seeing stolen your data increase at the same pace, if not your own accounts.
In fact, it often happens that your account can find itself subject to attacks by malicious people, with the risk of seeing your personal data (in addition to any credit cards registered to make payments) stolen and used. from the latter.
Of course, in the digital age, security tries to keep pace with progress and, if yesterday the only way to fix it was change often and willingly the password of the our accounts, always using different ones and following the classic guidelines to create them (presence of special characters, capital letters, numbers, various and any), fortunately today there are additional methods.
Of course, these methods do not make the precautions described above useless (it is always good to update the password, this remains the golden rule) but, adding to them, they insert additional levels of protection.
Companies such as Google and Microsoft (just to name a few of the most authoritative) have been guaranteeing their users for some time the possibility of recovering an account subject to attack, by entering a second email address in the security settings, address that will then be used in case of need.
Obviously, in this case, we are talking more about ploys to contain the damage than to prevent it.
And it is to prevent certain situations from occurring that, lately, new security features have been created at the account login level, which make theft considerably more difficult.
Today, in fact, we can choose to activate “two-step verification”.
Do you want to know how to increase visits to your website?
Book a free appointment online now.
What is it about?
In a nutshell, when we enter our account by entering the username and password, the system does not immediately allow us access, but first asks us for a second confirmation, by sending an authorization request to our second email address or even to our smartphone (if properly configured).
Virtually, this mechanism also doubles the difficulty in “piercing” our credentials and immediately warns us of the danger by promptly sending us an authorization request and allowing us to promptly assess whether it is was generated by us.
The steps to activate this second level of protection are simple: it is often offered to us directly when activating an account or with regular reminders when we log in.
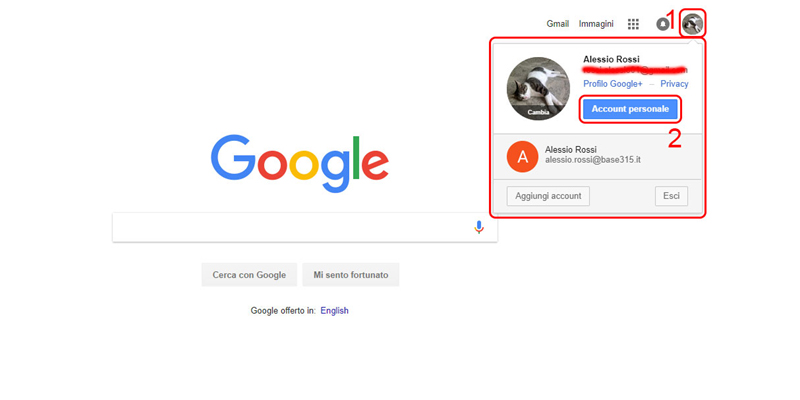
In any case, if you wish to activate it on Google, simply access the homepage and go to “personal account”.
Once this is done, you will have to select the item “access and security”.
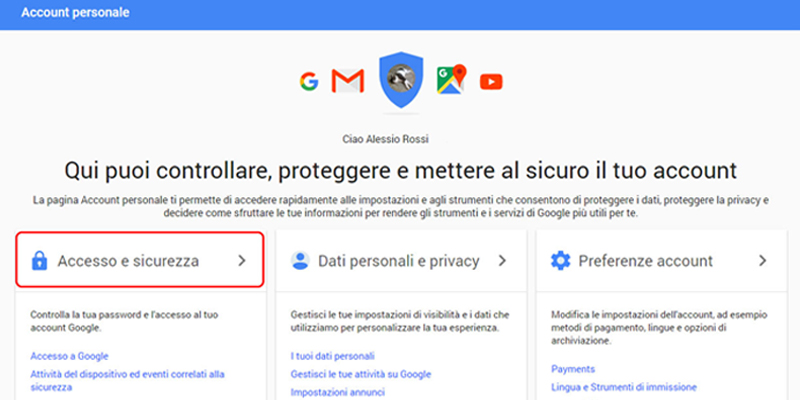
The page that opens will contain all the security functions for our account, which we can modify at will.
If our Android smartphone is synchronized with our Google account, we can decide to send the authorization request via push notification.
The same operation can be performed thanks to the Google Authenticator app, available both for:
If we have more than one account, we can obviously register them all in the app, one independently of the other.